Remus-Infostealer stiehlt Browser-Passwörter und umgeht Verschlüsselung von Anwendungen
Ein gefährliches neues Malware-Programm namens Remus ist aufgetaucht und nimmt dort an, wo einer der gefürchtetsten Informationsdiebe aufgehört hat.

Kurzfassung
Warum das wichtig ist
- Ein gefährliches neues Malware-Programm namens Remus ist aufgetaucht und nimmt dort an, wo einer der gefürchtetsten Informationsdiebe aufgehört hat.
- A dangerous new piece of malware called Remus has surfaced, quietly picking up where one of the most feared information stealers left off.
- Designed to steal browser passwords, cookies, and cryptocurrency wallets, Remus carries the DNA of Lumma Stealer, one of the most technically advanced stealers-as-a-service seen in recent history.
Remus first appeared in the wild around January and February 2026, arriving shortly after Lumma Stealer suffered a major disruption. Between late August and October 2025, alleged core members behind Lumma were exposed through a doxxing campaign that rattled the group’s operations. Researchers believe some of Lumma’s authors split off or chose to rebuild under a new name, and Remus appears to be the result.
Analysts at Gen Threat Labs identified this new threat, tracing its roots to test builds labeled as Tenzor. Dated September 16, 2025, those builds served as a bridge between Lumma and what would become Remus. Researchers Vojtech Krejsa and Jan Rubin attributed Remus as a new 64-bit variant of the Lumma family, noting that Lumma was originally a 32-bit operation.
What makes Remus especially concerning is how closely it mirrors Lumma in design and behavior. The two the same string obfuscation method, anti-virtual machine checks, nearly identical code structure, and a browser encryption bypass that researchers had only ever seen Lumma use. This level of overlap points strongly to a shared origin. While Lumma campaigns continue globally, Remus is not a direct replacement.
It is more of a natural
It is more of a natural evolution, upgrading the architecture to 64-bit and adding newer evasion techniques. Both threats represent a widening footprint for an actor that has already proven very hard to stop. Lumma-Style Browser Key Theft One of Remus’s most alarming inherited capabilities is its method for breaking into browser-protected data.
It targets Application-Bound Encryption, a security layer Chromium browsers use to protect sensitive keys stored on disk. Rather than reading the key off disk, Remus injects a small shellcode into the live browser process to locate and decrypt the master key from inside the browser’s own memory.
Remus decrypting the hex pattern used in the ABE bypass (Source – GenDigital) This technique had previously only been observed in Lumma Stealer. Remus searches for a specific byte pattern inside the browser’s code, locates the encrypted key in memory, and uses the browser’s own decryption functions to unlock it. The shellcode Remus injects is more compact at 51 bytes versus Lumma’s 62, suggesting active refinement.
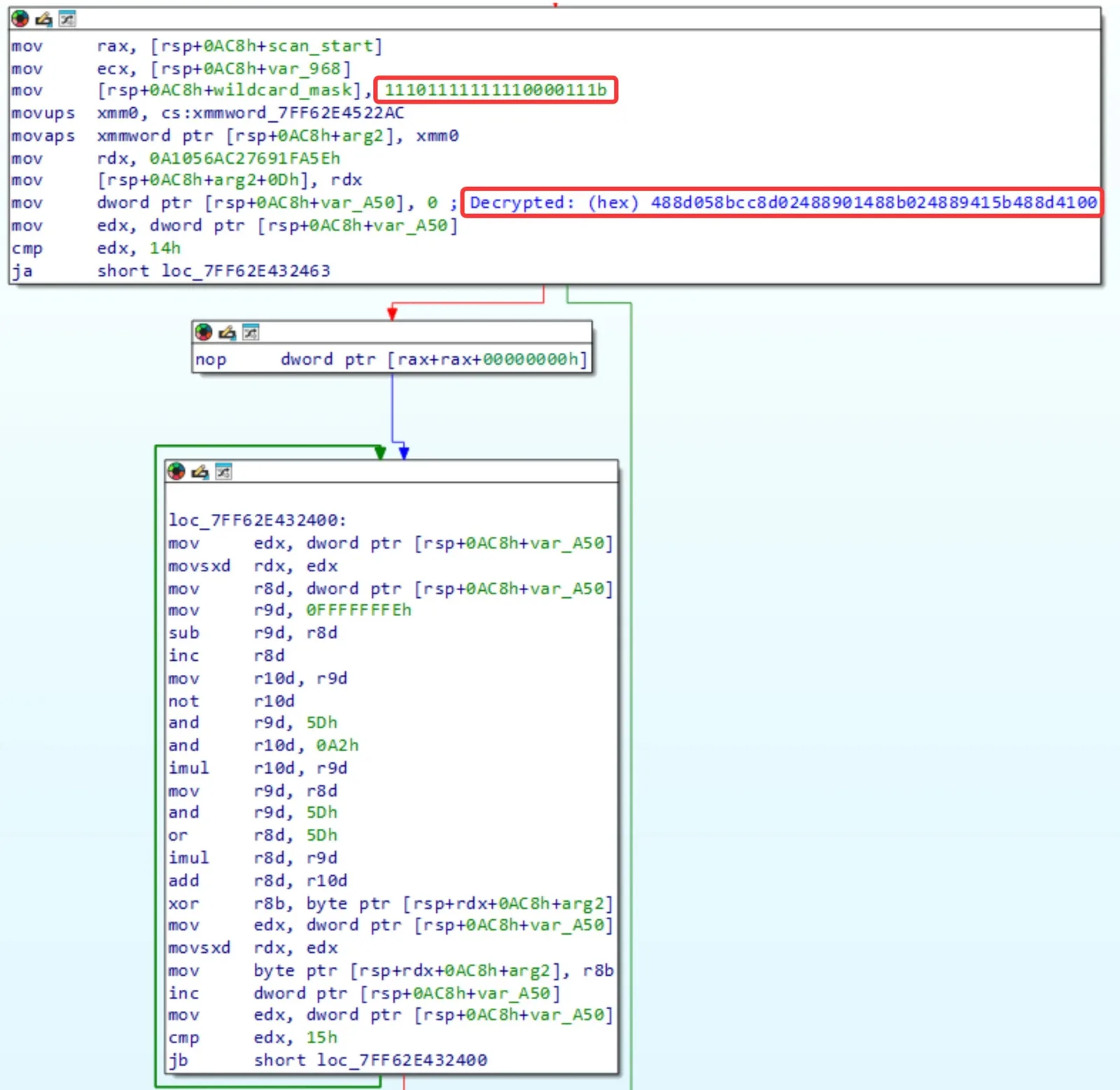
If injection into an existing browser
If injection into an existing browser process fails, Remus launches a hidden browser on a separate desktop, invisible to the user. Unlike Lumma, which used a hardcoded desktop name, Remus generates a random 16-character string each time. This makes detection harder for tools that rely on fixed naming patterns.
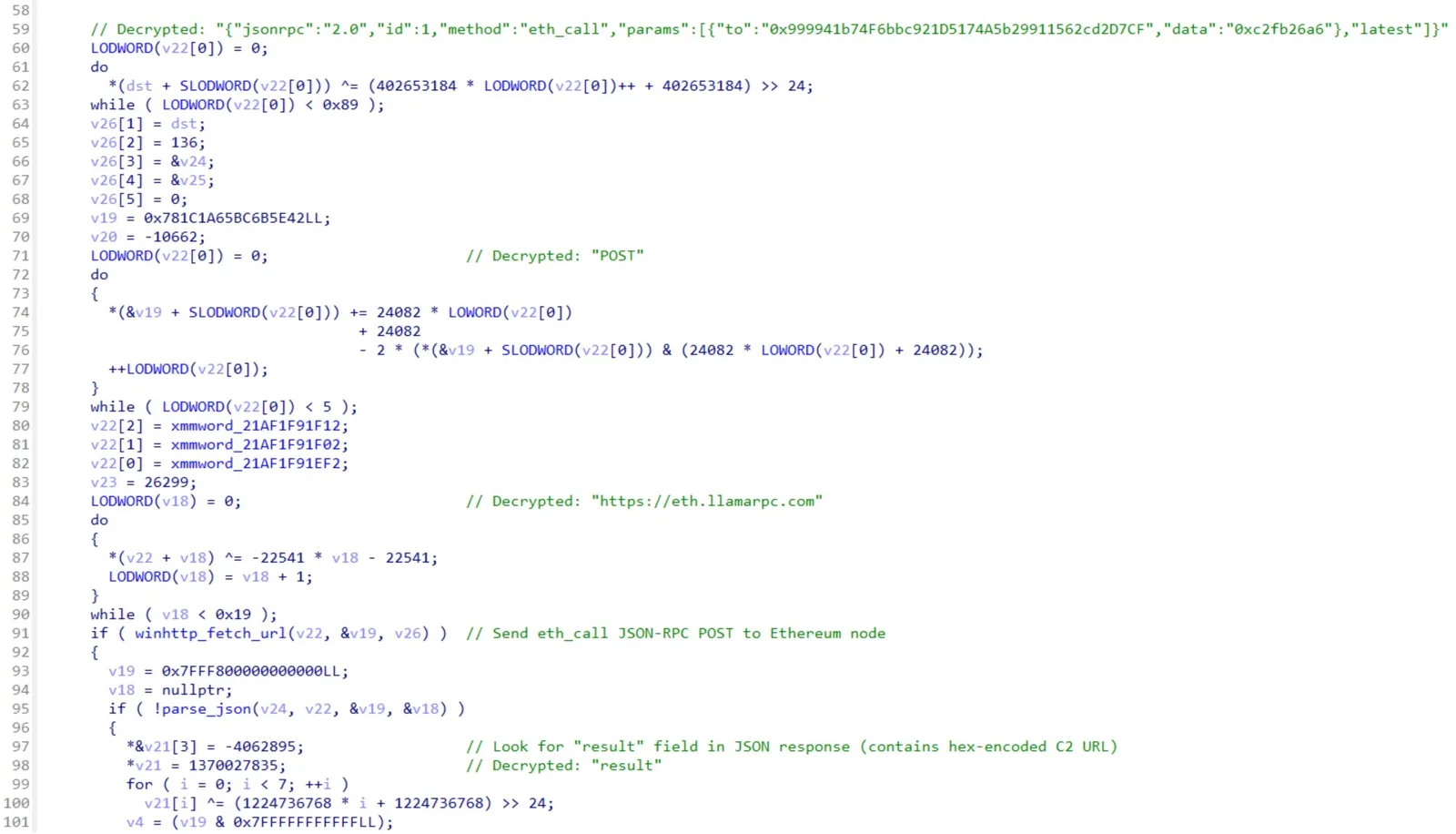
EtherHiding and Anti-Analysis Evasion Beyond encryption bypass, Remus introduces a key upgrade in how it contacts its command-and-control servers. Lumma relied on platforms like Steam and Telegram to store server addresses. Remus replaces this with EtherHiding, embedding the server address inside an Ethereum blockchain smart contract, making its infrastructure far harder to disrupt.
Remus resolving a C2 using EtherHiding (Source – GenDigital) Because blockchain data is decentralized and cannot be removed, there is no single point of failure for defenders to target. Remus queries the smart contract at runtime over a public endpoint and pulls the current server address, removing a defensive lever that had worked against Lumma.
Remus also adds checks to detect analysis tools and sandbox environments before executing. It scans for DLLs linked to known analysis platforms and checks for a specific honeypot file on disk. If either check triggers, the malware exits silently. These capabilities make Remus a stealthier and more sophisticated threat that security teams need to address without delay. on
Thema weiterverfolgen
Interne Verlinkung
Im Kontext weiterlesen
Diese weiterfuehrenden Links verbinden das Thema mit relevanten Archivseiten, Schlagwoertern und inhaltlich nahen Artikeln.
Technologie Archiv
Weitere Meldungen aus derselben Hauptkategorie.
Mehr von Cyber Security News
Alle veroeffentlichten Inhalte derselben Quelle im Archiv.
Apple Intelligence: Nutzer wählen künftig das KI-Modell für iOS 27
Redaktionell verwandter Beitrag aus dem selben Themenumfeld.
US-Test: Kernbrennstoff reduziert Abfall und hält achtmal länger
Redaktionell verwandter Beitrag aus dem selben Themenumfeld.
Quellenprofil
Quelle und redaktionelle Angaben
- Quelle
- Cyber Security News
- Originaltitel
- Remus Infostealer Uses Lumma-Style Browser Key Theft and Application-Bound Encryption Bypass
- Canonical
- https://cybersecuritynews.com/remus-infostealer-uses-lumma-style-browser-key-theft/
- Quell-URL
- https://cybersecuritynews.com/remus-infostealer-uses-lumma-style-browser-key-theft/
Aehnliche Inhalte
Verwandte Themen und interne Verlinkung
Weitere Artikel aus aehnlichen Themenfeldern, damit Leser direkt im selben Kontext weiterlesen koennen.
Apple Intelligence: Nutzer wählen künftig das KI-Modell für iOS 27
Apple plant mit iOS 27, Nutzern die Wahl des KI-Modells zu geben, das Apple Intelligence antreibt. Durch das neue Feature „Extensions“ können externe Modelle wie Googles Gemini und Anthropic's Claude systemweit auf iPhones, iPads und Macs integriert werden.
06.05.2026
Live Redaktion
US-Test: Kernbrennstoff reduziert Abfall und hält achtmal länger
ANEEL, ein neues Kernbrennstoffmaterial, Thorium und angereichertes Uran kombiniert, hat einen mehrjährigen Irradiationstest Advanced Test Reactor in den USA erfolgreich abgeschlossen.
06.05.2026
Live Redaktion
AMD erweitert EPYC-CPUs mit Zen 7: Mehr Spezialisierung und Anpassung für KI und Cloud
Moderne Rechenzentrumslasten sind sehr vielfältig, und ebenso unterschiedlich sind Anforderungen Betreiber .
06.05.2026
Live Redaktion
Elektro-Schiffe laden auf See kabellos: Neues Magnet-System revolutioniert die Energiezufuhr
Elektroautos verfügen über Ladesäulen entlang jeder wichtigen Straße, doch der maritime Sektor verfügt noch immer über kein praktikables Offshore-Ladenetzwerk.
06.05.2026
Live Redaktion